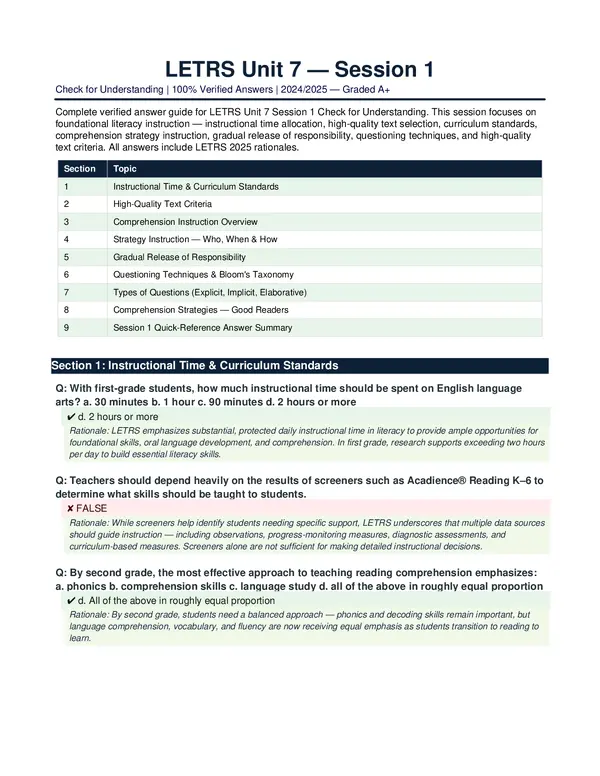
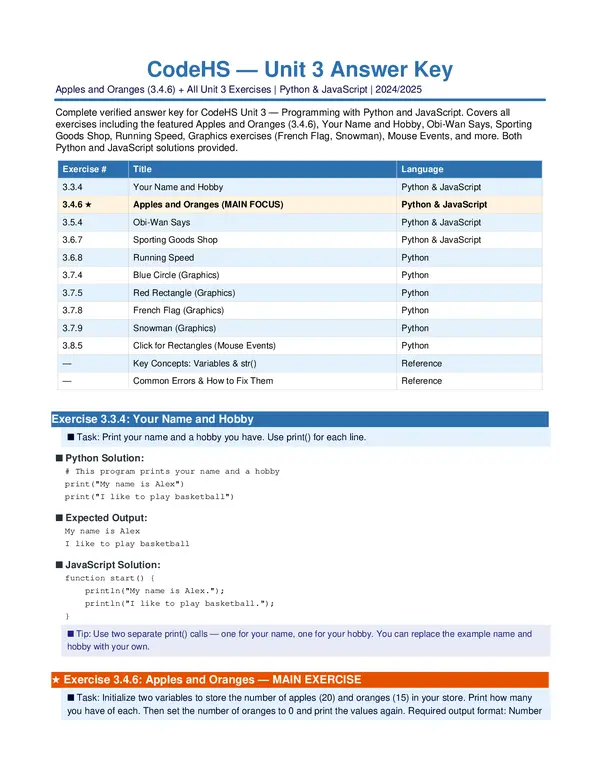
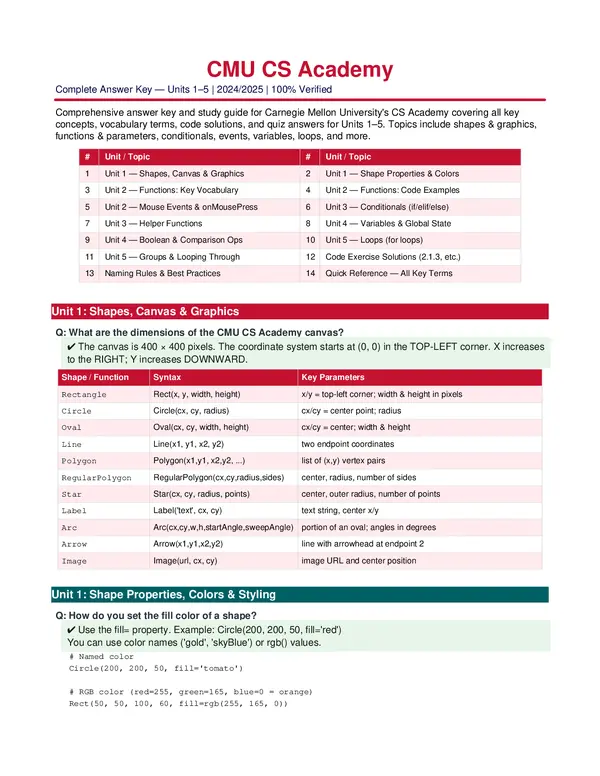
Level 1 Antiterrorism Awareness Training – PreTest JKO 2025/2026 Version, Exams of Security Analysis
/ 6
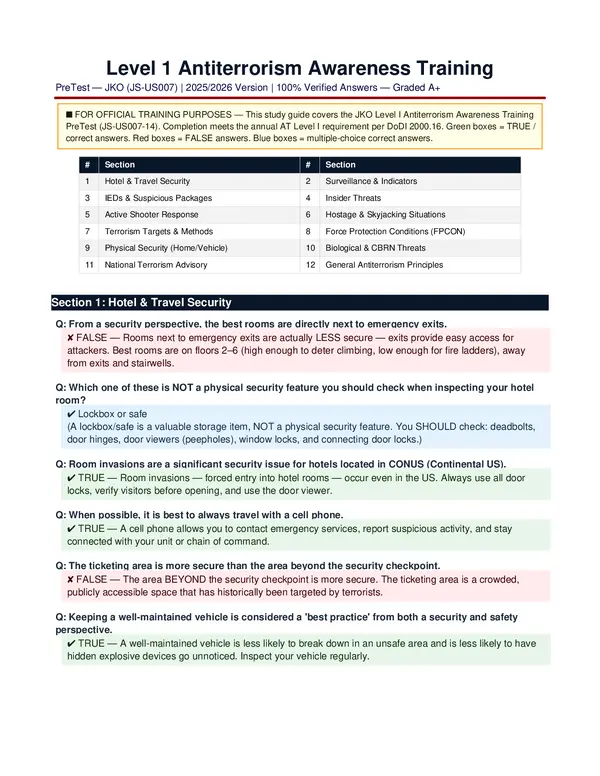
Level 1 Antiterrorism Awareness Training
PreTest — JKO (JS-US007) | 2025/2026 Version | 100% Verified Answers — Graded A+
■ FOR OFFICIAL TRAINING PURPOSES — This study guide covers the JKO Level I Antiterrorism Awareness Training
PreTest (JS-US007-14). Completion meets the annual AT Level I requirement per DoDI 2000.16. Green boxes = TRUE /
correct answers. Red boxes = FALSE answers. Blue boxes = multiple-choice correct answers.
# Section # Section
1 Hotel & Travel Security 2 Surveillance & Indicators
3 IEDs & Suspicious Packages 4 Insider Threats
5 Active Shooter Response 6 Hostage & Skyjacking Situations
7 Terrorism Targets & Methods 8 Force Protection Conditions (FPCON)
9 Physical Security (Home/Vehicle) 10 Biological & CBRN Threats
11 National Terrorism Advisory 12 General Antiterrorism Principles
Section 1: Hotel & Travel Security
Q: From a security perspective, the best rooms are directly next to emergency exits.
✘ FALSE — Rooms next to emergency exits are actually LESS secure — exits provide easy access for
attackers. Best rooms are on floors 2–6 (high enough to deter climbing, low enough for fire ladders), away
from exits and stairwells.
Q: Which one of these is NOT a physical security feature you should check when inspecting your hotel
room?
✔ Lockbox or safe
(A lockbox/safe is a valuable storage item, NOT a physical security feature. You SHOULD check: deadbolts,
door hinges, door viewers (peepholes), window locks, and connecting door locks.)
Q: Room invasions are a significant security issue for hotels located in CONUS (Continental US).
✔ TRUE — Room invasions — forced entry into hotel rooms — occur even in the US. Always use all door
locks, verify visitors before opening, and use the door viewer.
Q: When possible, it is best to always travel with a cell phone.
✔ TRUE — A cell phone allows you to contact emergency services, report suspicious activity, and stay
connected with your unit or chain of command.
Q: The ticketing area is more secure than the area beyond the security checkpoint.
✘ FALSE — The area BEYOND the security checkpoint is more secure. The ticketing area is a crowded,
publicly accessible space that has historically been targeted by terrorists.
Q: Keeping a well-maintained vehicle is considered a 'best practice' from both a security and safety
perspective.
✔ TRUE — A well-maintained vehicle is less likely to break down in an unsafe area and is less likely to have
hidden explosive devices go unnoticed. Inspect your vehicle regularly.

Q: State Department Travel Warnings should be consulted prior to taking trips across the US-Mexican
border.
✔ TRUE — Always check the latest State Department Travel Advisories before traveling — both
internationally and to high-risk border areas.
Section 2: Surveillance & Indicators of Terrorist Activity
Q: Surveillance can be performed through either stationary or mobile means.
✔ TRUE — Terrorists conduct surveillance using BOTH stationary observation (watching from a fixed location)
and mobile surveillance (following targets by vehicle or on foot).
Q: Electronic audio and video devices are never used by terrorists for surveillance purposes.
✘ FALSE — Terrorists DO use electronic devices — cameras, audio recorders, and even drones — to conduct
surveillance and gather intelligence on targets.
Q: What is NOT a terrorist method of surveillance?
✔ Breaking and entering to steal valuables
(Theft is a criminal activity, not typically a terrorist surveillance method. Terrorist surveillance methods include:
photography, video recording, note-taking, asking questions, and monitoring patterns of activity.)
Q: If you identify a possible surveillance attempt, you should try to handle the situation yourself.
✘ FALSE — Do NOT confront suspected terrorists yourself. Report suspicious activity to law enforcement or
your chain of command immediately. Confronting suspects puts you at risk.
Q: Which one of these does NOT pose a risk to security at a government facility?
✔ A person expressing boredom with the US mission
(Boredom alone is not an indicator of a security threat. Genuine risks include: unauthorized photography,
asking unusual questions about security measures, lingering without purpose, or attempting to access
restricted areas.)
Q: Internet acquaintances can pose a security threat and should be carefully monitored.
✔ TRUE — Terrorists and foreign intelligence services use social media and online platforms to recruit, gather
information, and identify vulnerabilities. Be cautious about what you share online.
Section 3: IEDs & Suspicious Packages
Q: IEDs may come in many forms and may be camouflaged to blend in to the surrounding environment.
✔ TRUE — Improvised Explosive Devices (IEDs) have been disguised as roadside debris, trash bags,
abandoned vehicles, packages, and even everyday objects. Never approach suspicious items.
Q: Which one of these is a possible indicator of a suspicious letter or package?
✔ Misspellings of common words
(Other indicators include: no return address, excessive postage, oily stains or discoloration, strange odors,
unusual weight, rigid or lopsided envelope, wires or aluminum foil visible, and unexpected origin.)
Q: What should you do if you find a suspicious package?
✔ Do NOT touch it — move away, clear the area, and report it to security/law enforcement immediately
(The 3 Rs: Recognize, Retreat (don't touch), Report. Never attempt to open or move the package. Keep others
away and wait for trained personnel.)
Section 4: Insider Threats

Q: From an antiterrorism perspective, espionage and security negligence are considered insider threats.
✔ TRUE — Insider threats include espionage (spying), sabotage, theft, unauthorized disclosure, and security
negligence. Anyone with authorized access who misuses it poses an insider threat.
Q: From an antiterrorism perspective, espionage and security negligence are NOT considered insider
threats.
✘ FALSE — This is the FALSE version of the same concept — both espionage AND security negligence ARE
insider threats under the DoD definition.
Q: Which one of the following is NOT an early indicator of a potential insider threat?
✔ A reasonable disagreement over US Government policy
(Reasonable policy disagreement is a protected expression of opinion — it is NOT an insider threat indicator.
Actual indicators include: abnormal mood swings, depression, suicidal remarks, presence of unauthorized
weapons, aggression or threats toward coworkers, and sudden unexplained wealth.)
Q: Knowing indicators of an unstable person can allow you to identify a potential insider threat before an
incident.
✔ TRUE — Early recognition of behavioral warning signs — such as extreme mood changes, expressions of
grievance, unusual interest in security systems, or threats — can help prevent incidents.
Q: Persons who have been given access to an installation can be counted on to be of no threat.
✘ FALSE — Access does NOT equal trustworthiness. Insider threats often come from authorized personnel.
Always remain vigilant and report suspicious behavior through proper channels.
Section 5: Active Shooter Response
Q: Active resistance should be the immediate response to an active shooter incident.
✘ FALSE — The preferred response order is: RUN (escape if possible) → HIDE (barricade/shelter) → FIGHT
(actively resist only as a last resort when your life is in immediate danger).
Q: In an active shooter incident involving firearms, you should immediately lie on the ground.
✘ FALSE — Lying on the ground makes you a stationary target. Instead: RUN if a clear escape route exists,
HIDE behind solid cover if you cannot escape, or FIGHT as a last resort.
Q: Which of the following is NOT a recommended response to an active shooter incident?
✔ Provide instructions to arriving law enforcement personnel or stop them to ask for help
(When law enforcement arrives, DO NOT: stop them, give them instructions, or try to help them. Instead: keep
your hands visible, follow all commands, and do not make sudden movements. Let professionals take control.)
Q: Which of the following IS a recommended response to an active shooter?
✔ Look for a place to hide or an area that can be barricaded / Look for possible escape routes / Find
something solid to take cover behind / If necessary, actively resist as a last resort
(The Run-Hide-Fight protocol: Escape if possible, barricade/hide if you cannot escape, and fight only when
there is no other option to survive.)
Section 6: Hostage Situations & Skyjacking
Q: The initial moments of a hostage taking incident can be extremely dangerous.
✔ TRUE — The first few minutes of a hostage incident are the most dangerous — captors are agitated and
may react violently. Stay calm, comply with instructions, and avoid confrontation.
Loading document...
/ 6
Upload to Download
Every 3 documents you upload earns 1 download credit.
You have uploaded 0 documents. Upload 3 more to earn a download.
Upload Documents