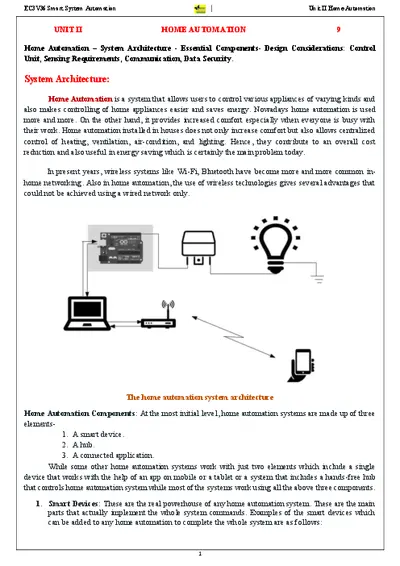
EC3V36 Smart System Automation Unit II Home Automation
3
Three steps are followed in home automation as follows:
1. Monitoring: This means keeping the control of the system using an app on a device remotely.
2. Control: This means that the system can be controlled remotely from anywhere through the app by the user.
3. Automation: Automation means making almost all devices automatic for making it a better system.
Applications: Some of the most common applications of home automation are as follows-
➢ Heating, ventilation, and air conditioning.
➢ Lighting control system.
➢ Occupancy-aware control system.
➢ Leak detection.
➢ Smoke sensors.
➢ Indoor positioning systems.
➢ Home automation for the elderly and disabled.
➢ Air quality control.
➢ Smart Kitchen.
➢ Connected Cooking.
➢ Voice control devices like Amazon Alexa or Google Home used to control home appliances or systems etc.
Security And Privacy Concern: The security and privacy of any home automation system are at the top
level for keeping the working of home automation smoothly. So, there are some steps or knowledge it can
be achieved easily and vastly which are as follows:
➢ Privacy Policy: Read the privacy policy carefully and know each and every point about how they
share it and sell it to third parties.
➢ Naming of Router: Be sure to give your router a name except for the name it came with when get
purchased.
➢ Encryption: Select an end-to-end encrypted method for your Wi-Fi, like WPA2.
➢ WiFi Password: Make separate passwords for each Wi-Fi connection to your devices.
➢ Separate WiFi Network: For the most security for your IoT devices use a separate Wi-Fi network
for IoT devices only. This will also create faster Internet speeds all around.
➢ Password: Make your home automation password protected. Choose a strong password for the
Wi-Fi network.
➢ Device settings: Devices have features enabled by default that are not necessarily required so, turn
it off when these features are not in use like Wi-Fi, Bluetooth, and knowing your location i.e.
Location Tracking feature.
➢ Software Updates: The software update is also the most important step in security because it
performs all the steps needed for security or privacy concerns.
➢ Authentication: Using a two-factor authentication system will help a lot because by this the
password or any kind of verification first comes to your mobile phone then only any application gets
opened.
➢ VPN: It stands for Virtual Private Network. If VPN is being used or any other public network for
connection, then hide your IP address.